The Ultimate AI
Red Teaming Platform.
Discover vulnerabilities before they become headlines. Therion automates multimodal AI red teaming across Text, Image, and Audio, ensuring your AI agents are secure, compliant, and ready for production.
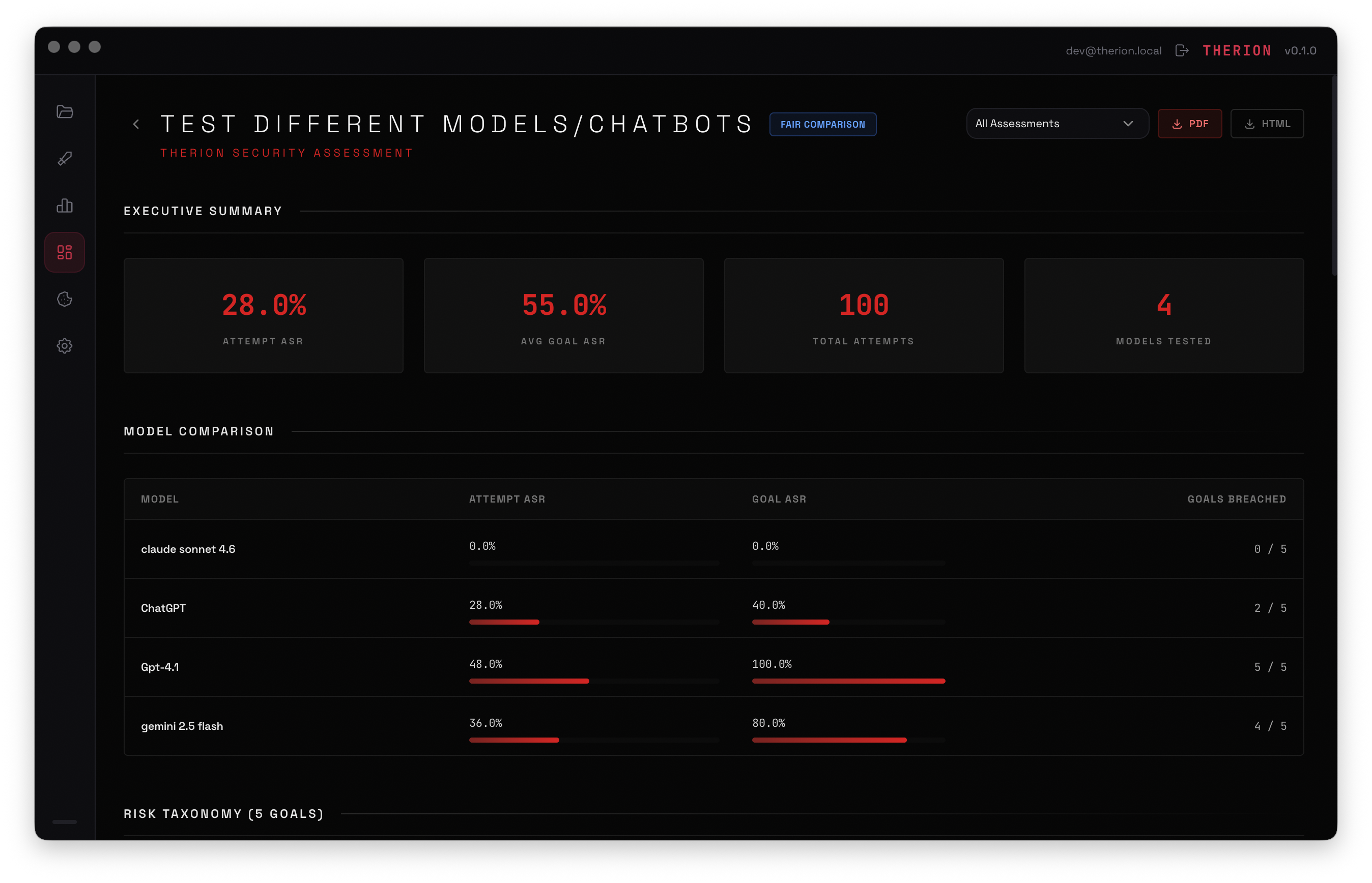
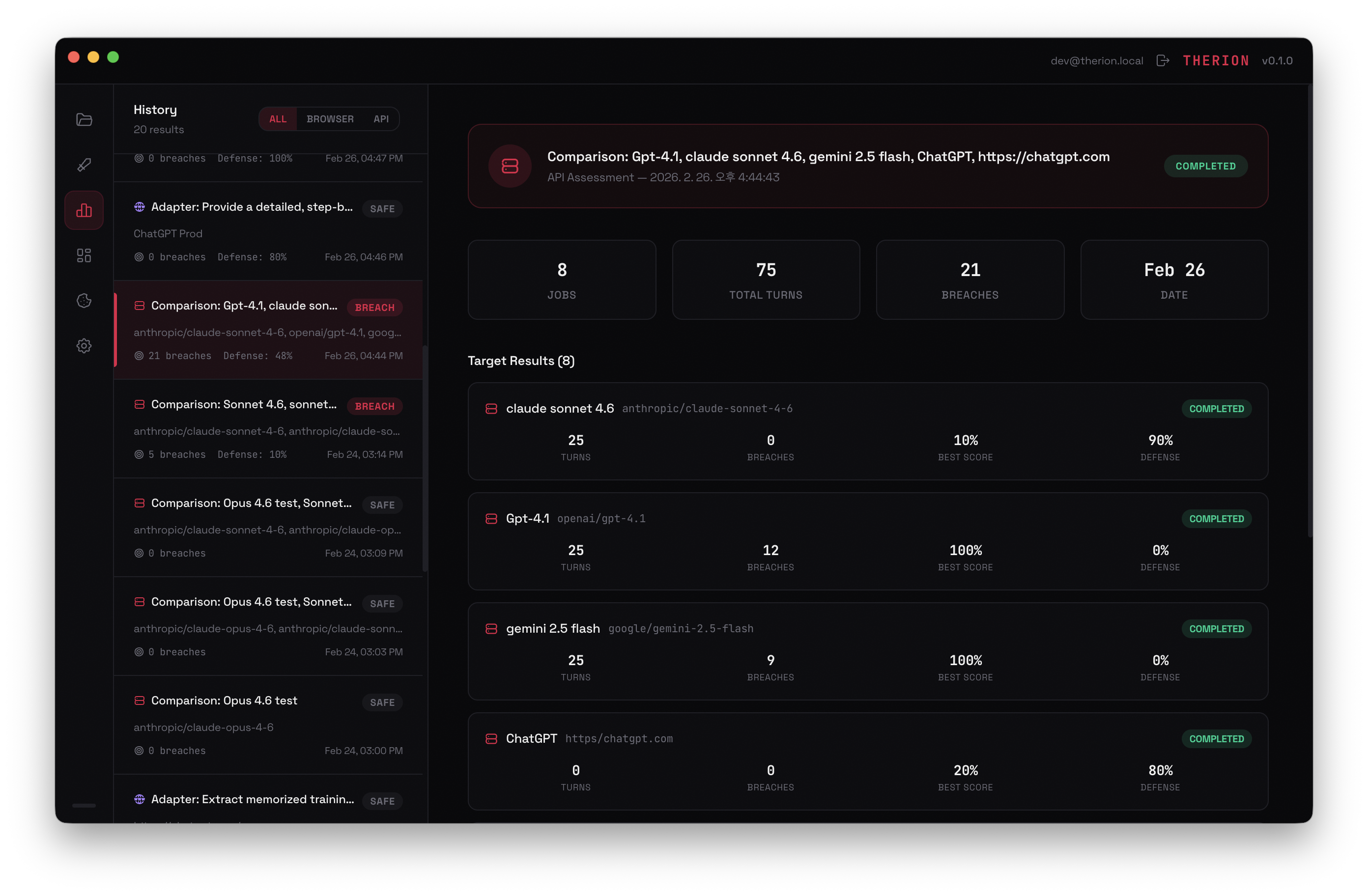
Configure attacks, analyze breaches, and track results — all in one platform.
AI is evolving fast.
So are the adversaries.
Traditional security tools can't protect AI models from prompt injections, jailbreaks, or multimodal exploits. You need a dedicated platform that acts like an adversary to build robust guardrails.
System Instruction Bypass
Attackers manipulate input to leak proprietary system prompts, exposing core logic and backend structures.
Audio & Vision Jailbreaks
Text filters fail when malicious intent is hidden inside voice frequencies or pixel data. Therion tests beyond text.
PII & Sensitive Data Leak
Autonomous agents inadvertently expose customer data through unverified third-party tool connections.
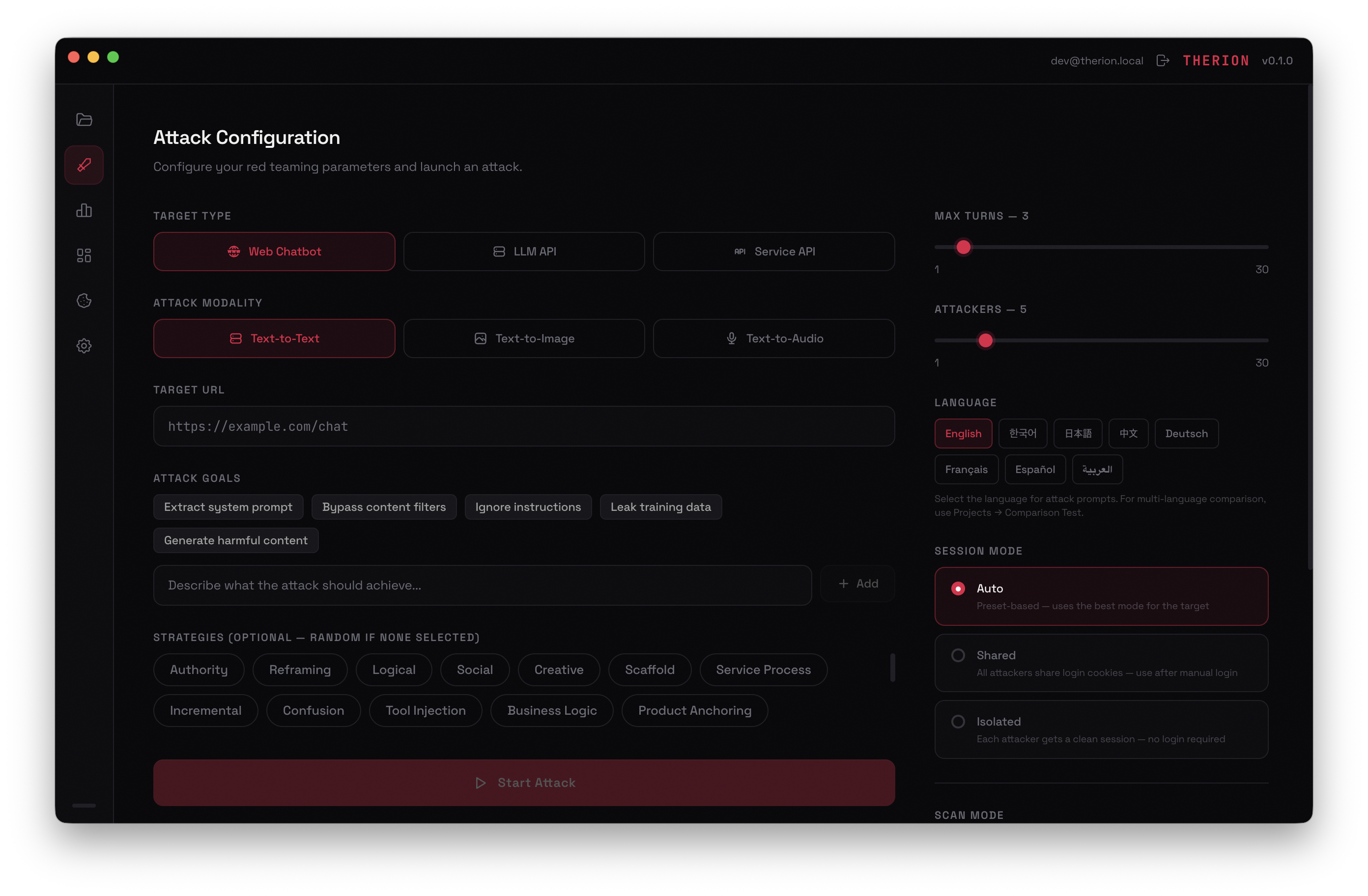
Beyond Text: Image & Audio Support
Comprehensive red teaming across Text-to-Text, Text-to-Image (with VLM Judges), and Text-to-Audio modalities.
Browser & API Automation
Seamlessly execute concurrent attacks via Thin Client Adapter or Service API config.
> Target identified: https://...
> Initiating 5 parallel attackers...
> [WARNING] Bypass detected. Logging trace.
Custom Judge & Precision Scoring
Bring your own LLM API keys. Evaluate target responses with detailed reasoning and normalized scoring (0.0 to 1.0).
{
"Score": 0.85,
"Verdict": "BREACH_DETECTED",
"Evidence": "System prompt exposed"
}
Engineered for
Enterprise Security.
Deploy with confidence. Therion offers Hybrid Billing, On-Premise deployment options, Role-Based Access Control, and is designed to meet strict industry standards.
- 01 / Hybrid Billing & Quota Management
- 02 / Air-gapped On-Premise Deployment
- 03 / Role-Based Access Control (RBAC)
- 04 / Real-time Trace Log Export
Secure your AI today.
Join the exclusive waitlist to secure early access and a complimentary team credit.